Operation Serengeti, a massive coordinated effort between law enforcement agencies across Africa, dealt a crushing blow to cybercriminals, arresting over 1,000 suspects and dismantling more than 134,000 malicious networks.
A joint mission by INTERPOL and AFRIPOL, it unveiled the dark underbelly of cybercrime between September and October 2024, revealing just how sophisticated and far-reaching digital criminal networks have become.
Take Kenya, for instance. Cybercrime investigators uncovered a vast fraud scheme involving $8.6 million in stolen funds. The criminal group’s method was almost cinematic: they infiltrated banking system security protocols, running fraudulent scripts that siphoned money with incredible precision.
Once the criminal syndicate gained access to banking systems, they quickly redistributed the stolen funds via SWIFT transfers to companies spanning the United Arab Emirates, Nigeria, and China, and then to digital asset trading platforms across multiple jurisdictions. Thankfully, the joint operation made over two dozen arrests and disrupted the highly organized criminal network.
Kenya wasn’t alone. Across the continent, remarkable takedowns were happening as well.
- In Senegal, eight people, including five Chinese nationals, were arrested for a $6 million online Ponzi scheme that affected 1,811 victims. Investigators found over 900 SIM cards, $11,000 in cash, and copies of victims’ identification cards in their apartment.
- Nigeria nabbed an online investment scammer believed to have made over $300,000 by luring victims with false cryptocurrency promises.
- Cameroon uncovered a shocking human trafficking scheme disguised as a multi-level marketing operation, where victims were held captive and forced to recruit others.
- Angola dismantled an international virtual casino ring that had defrauded hundreds of Brazilian and Nigerian gamblers, resulting in 150 arrests and the seizure of 200 computers.
INTERPOL’s Secretary General, Valdecy Urquiza, commented on the growing cybercrimes, stating, “From multi-level marketing scams to credit card fraud on an industrial scale, the increasing volume and sophistication of cybercrime attacks is of serious concern.” AFRIPOL’s Executive Director, Ambassador Jalel Chelba, also highlighted the rise of AI-driven malware and advanced attack techniques as an emerging concern.
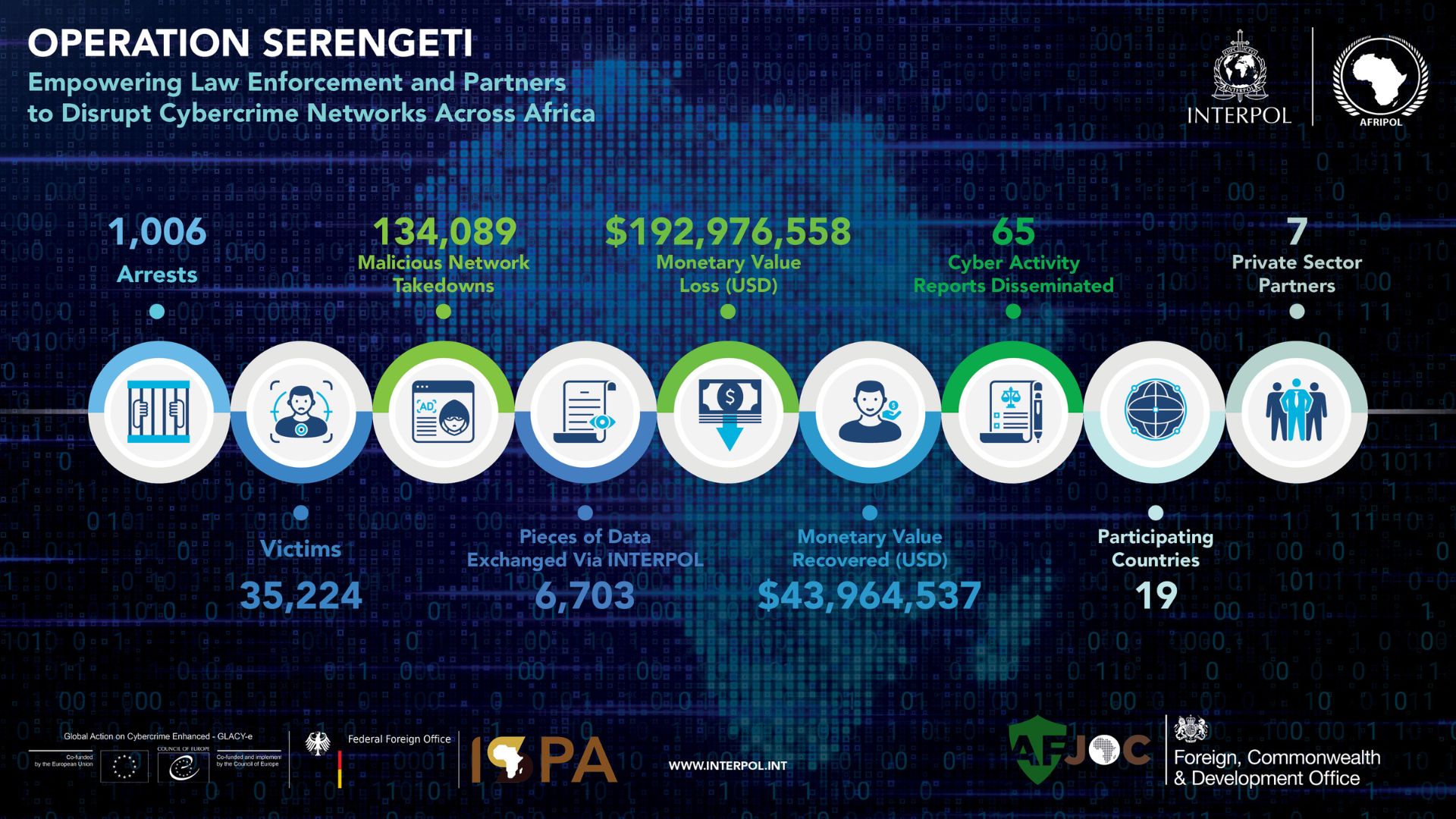
Beyond the arrests, private sector partners, including Internet Service Providers (ISPs), played a crucial role by sharing intelligence, supporting analysis, and helping secure critical infrastructure. The operation was funded by the UK’s Foreign, Commonwealth and Development Office, the German Federal Foreign Office, and the Council of Europe.
With more than 35,000 victims identified and nearly $193 million in global financial losses linked to these cases, Operation Serengeti is just one example of the numerous digital threats lurking in our interconnected world.
























