That you or your device, regardless of platform, are not safe online is not something new. It has been proven time and again that mobile devices are as vulnerable to attacks as other computing devices have over the years.
Particularly, Android devices have borne the brunt of most exploits recently. For instance, in July last year, security firm Zimperium announced that it had discovered a deadly vulnerability in Android. The vulnerability, which went on to be known by its nickname “Stagefright” affected virtually any device with a text messaging application meaning that over a billion devices running Android were at risk of malware injection through most major mobile messaging apps including Google’s own Hangouts.
Last month, security research firm Check Point announced the existence of HummingBad (Lookout, another security research firm, called it Shedun), a vulnerability originating from China which used a legitimate ad network to attack devices that visited certain websites and attempted to gain root access all the while spying on the users of such devices. Over 10 million Android devices belonging to various users were said to have been affected with several Asian countries (India, Indonesia, China and the Phillipines) topping the list of nations where users most fell at risk.
Fast forward a month later, Check Point announced yesterday at a major security conference of the existence of yet another equally bigger exploit codenamed Quadrooter.

According to the firm, the vulnerability lies in the special code included in Qualcomm devices that can be taken advantage of by third party applications if a user is tricked into installing them resulting in the said apps getting access to elevated privileges (root) and as a result able to do just about anything any person with ill/malicious intent would want them to do.
Over 900 Million Android devices are affected by Quadrooter
The vulnerability appears to be limited to just devices running Android and powered by Qualcomm’s mobile Snapdragon processors. Being the industry leader in the mobile chip-making business, this means that 80% of all Android devices are susceptible to attacks this way. Even the smartphone touted to be “the most secure smartphone on the planet”, the recently-unveiled BlackBerry DTEK50, is not immune to this, it’s equally affected.
Since Qualcomm was notified of the exploit’s existence by Check Point over 90 days ago, as is considered an industry best practice before announcing publicly, it has already released a patch to its various partners (device makers) who will, in turn, make it available to their users in about a month’s time. So there’s no need for alarm. Since the vulnerability can only be exploited if a rogue app is installed, those who’ve never strayed from the Play Store should be the last to be worried. Unless, of course, you’ve been downloading the many imitations that always manage to escape the Play Store’s checks and somehow find their way to the platform. Some of the flaws have already been fixed in the monthly security patches that Google releases. Still, better safe than sorry.
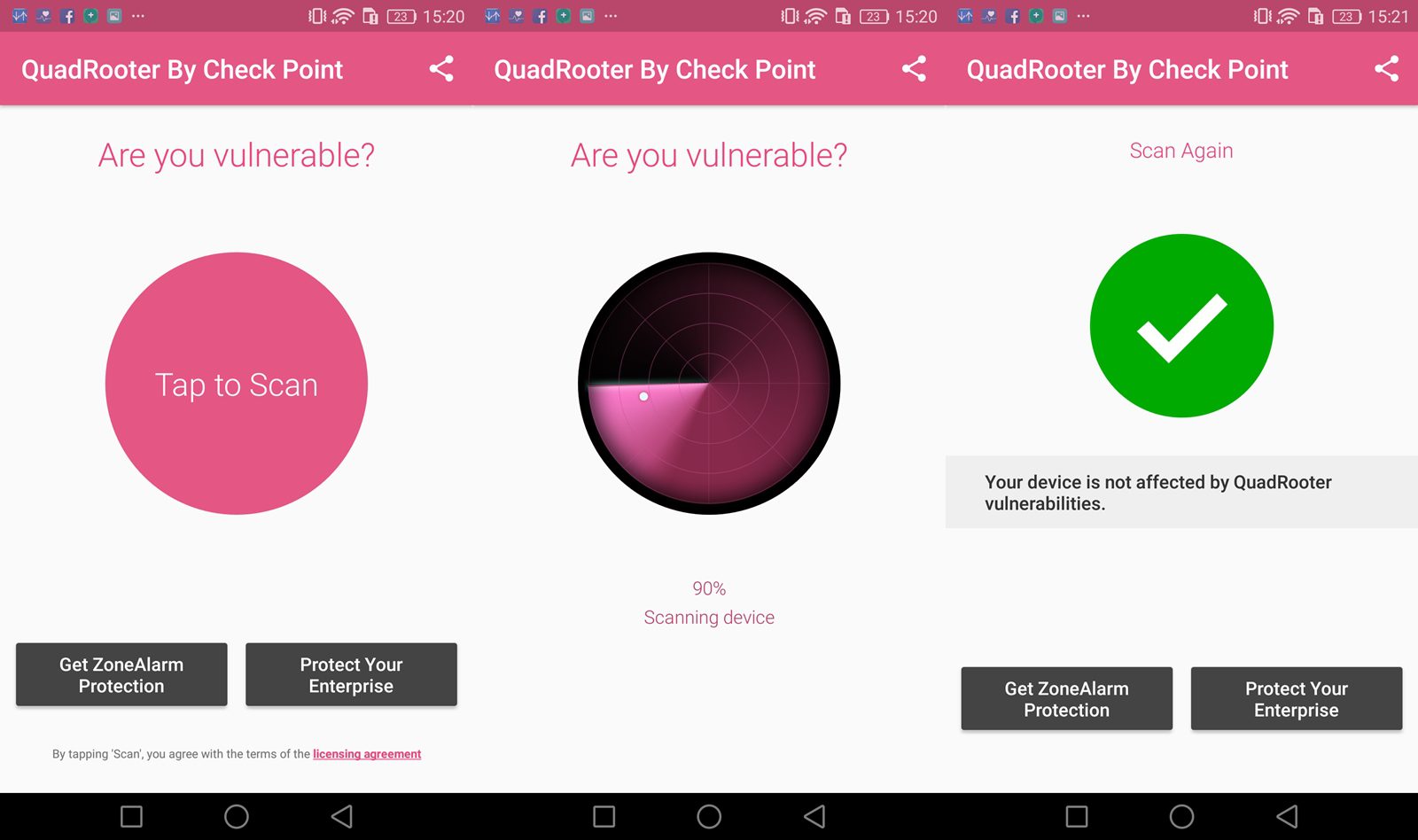
Check Point has provided an app that makes it easier to find out if your device is one of the 900 million said to be affected.