The majority of us are Instagram users, and it is possible that some of us know how easy it is for other people to steal content and present it as their own.
To note, this does not entail links, shares, retweets, and so on, which are legitimate ways for people to re-promote one’s work.
Rather, this is about outright scraping, copying, or republishing original content by someone else, as though they created the material themselves.
Often, this is done without permission from the original publisher.
In the same breath, you’ll also know how easy it is to end up being accused of copyright wrongdoing yourself, even if you’re always careful only to use third-party material in accordance with the original creator’s licensing guidelines.
So, given the frequent issues that surround online copyright issues, many social networks have established formal procedures for making complaints and appealing against takedowns.
Instagram’s procedures, for example, are listed in some detail on its official help page, which explains both how to complain if you think your content has been stolen, and how to respond if you’ve been falsely accused.
The Cybercrime Angle
Cybercriminals have learned how to use copyright infringement notices as bait in phishing scams.
By pretending to be a social network such as Instagram, they try to scare you into thinking that there’s an official copyright complaint against you, whilst at the same time giving you a quick and easy way of replying with a counter-claim of your own.
The criminals know that the complaint is totally bogus, and they know that you know it’s bogus.
But instead of leaving you to figure out that it’s bogus because there was no complaint in the first place, they trick you into thinking that the complaint was real, but that the bogus part was the accusation made by the complainer.
To do this, they don’t accuse you themselves, and they don’t threaten to sue; instead, they offer you an easy way to “prove” your “innocence” by providing a link to object to the “complaint”.
Some received copyright phishes are much more believable – and better spelled, and more grammatical – than many of the examples
Look at the example below:

The [Appeal] button in this example uses a shortened link (this one comes from bit.ly), but whether you check the destination of the link in advance or click through anyway, the resulting website doesn’t look as bogus as you might expect.
To check a bit.ly link before visiting it, paste the link into your browser’s address bar and add a plus sign (+) at the end, which tells bit.ly to show you the original link without redirecting to it.
Nevertheless, the crooks have registered the fake-but-not-too-far-off domain name fb-notify DOT com, and the link you’re given takes you to a personalized scam page that explicitly references your account:

In the screenshot above, the account statistics are correct, and the image shown does indeed come from the reported Instagram page (amusingly, and ironically, that means the email itself infringes copyright.)
In other pages linked to by these scammers, the image ripped off by the crooks always seemed to be scraped from the second-to-last post on the victim’s Instagram page.
That might have been a coincidence, or it could be a deliberate ploy by the crooks to pick an image recent enough that you’ll remember posting it, but not so recent that the copyright complaint might seem unrealistically quick.
The Sting
Anyone who gets this far is almost certainly starting to believe the scam, which would make the next page seem unexceptionable enough, especially given the HTTPS padlock and the sort-of-OK-looking fb-notify domain name:

The website then pretends you made an error typing in your password and tells you to try again, presumably as a simple way for the crooks to discard login attempts where a user clearly just bashed out any old garbage on the keyboard to see what happened next:

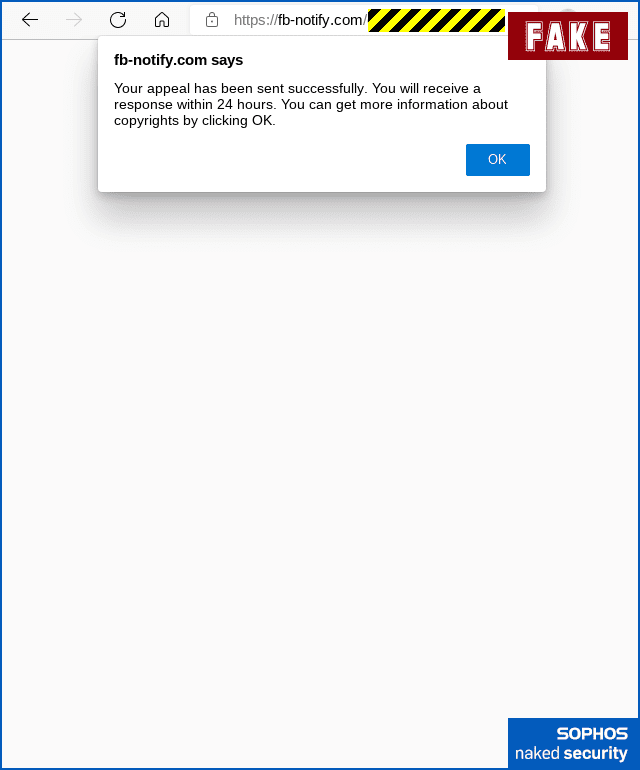
Then there’s a believable enough message to tell you that your appeal was submitted successfully:
Finally, the criminals sneakily redirect you to the real Instagram copyright page that we listed above, presumably to add an air of legitimacy that leaves you on a genuine website:

Be On The Lookout
Don’t click “helpful” links in emails. Learn in advance how to handle Instagram copyright complaints, so you know the procedure before you need to follow it. Do the same for the other social networks and content delivery sites you use. Don’t wait until after a complaint arrives to find out the right way to respond. If you already know the right URL to use, you never need to rely on any link in any email, whether that email is real or fake.
Think before you click. Although the website name in this scam is somewhat believable, it’s clearly not instagram.com or facebook.com, which is almost certainly what you would expect. Hopefully, you wouldn’t click through in the first place, but if you do visit the site by mistake, don’t be in a hurry to go further. A few seconds to stop and double-check the site details would be time well spent.
Use a password manager and 2FA whenever you can. Password managers help to prevent you from putting the right password into the wrong site because they can’t suggest a password for a site they’ve never seen before. And 2FA (those one-time codes you use together with a password) make things harder for the crooks because your password alone is no longer enough to give them access to your account.
Finally, talk to a friend you know face-to-face who’s done it before. If you are active on social media or in the blogosphere, you might as well prepare in case you ever get a copyright infringement notice for real. (We’re assuming the accusation will be false, but the complaint itself will actually exist.) If you know someone who has already gone through the genuine process once, see if they’ll tell you how it went in real life. This will make it much easier to spot fake complaints in the future.




























