Ransomware can severely disrupt systems by encrypting your files and demanding ransom for access. While personal computers are less likely targets, taking preventive measures is crucial. Enabling Windows’ built-in ransomware protection and keeping backups of essential files are practical steps to mitigate the risk. As seen with groups like Scattered Spider, ransomware can be devastating, even on a large scale. For instance, this group managed to bring Las Vegas casinos to a halt, causing millions in damage.
While large corporations are often targeted, personal computers are not immune, making it crucial to adopt preventive measures. . Windows Defender offers built-in ransomware protection, but it’s also essential to regularly back up your files and maintain up-to-date security software.
How ransomware works
- File Encryption: It encrypts files, making them inaccessible.
- Ransom Demands: Attackers often demand cryptocurrency, making it harder to trace payments.
- Widespread Impact: From individuals to major companies, ransomware can cripple entire operations.
Steps to Protect Yourself:
- Enable Controlled Folder Access: On Windows, this feature blocks unauthorized apps from accessing important files.
- Regular Backups: Ensure you back up critical files to an external drive or cloud service that ransomware can’t reach.
- Email Vigilance: Avoid opening suspicious attachments or links, as email phishing is a common ransomware delivery method.
- Antivirus and Updates: Keep your antivirus software updated and ensure your operating system is patched regularly to fix vulnerabilities.
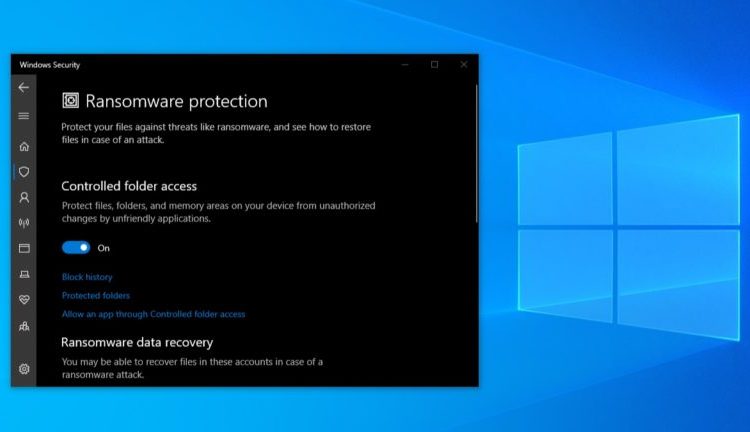
To turn on built-in ransomware protection on Windows:
- Go to Settings > Update & Security. Open the Windows Security app on your PC. You can access it in one of several ways: Press Alt + Spacebar on your keyboard, type in windows security, then hit Enter. Open your Start Menu and type in windows security, then press Enter, Open your Settings app, then choose Windows Security in the left pan
- Click on Windows Security in the sidebar.
- Select Virus & threat protection.
- Scroll down and click on Manage ransomware protection under the “Ransomware protection” section.
- Toggle Controlled folder access to “On.”
This setting restricts app access to your PC’s default OneDrive, Documents, Pictures, Videos, Music, and Favorites folders. You can also manually add other folders to the list.
Not all apps are automatically blocked from accessing protected folders in Windows’ Controlled Folder Access. For instance, Microsoft Office programs are trusted by default and can open and modify files in these locations.