
At last week’s The Web Conference researchers presented data that emphasized the importance of adding extra protection to your Google account. The researchers found out that a simple step such as adding a recovery phone number to your account blocked 100% of automated attacks, 99% of bulk phishing attacks and up to 66% of targetted attacks during the time of their investigations.

SMS verification isn’t the most safest as it too can be defeated by a targetted attack but Google has the ability to send a prompt to a connected phone and also have users verify their last logins that aid in blocking suspicious logins. More scrutiny, however, will be expected on logins from new devices or new locations.
Another type of attack is the hack for hire attacks which mimic Google itself or impersonate familiar people. These attacks are rare but can include multiple attempts even after the rejected initial message. Google already has steps such as its Advanced Protection Program where users are required to set up two hardware keys and one of them to log in all the time.
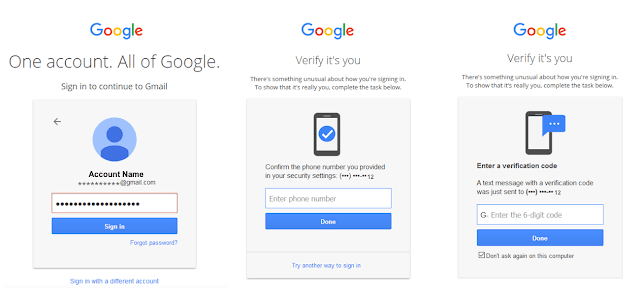
Hackers will go the extra length to get access to your personal data. Passwords can be leaked or easily be figured by malicious actors so it’s high time to protect your accounts with 2FA as an additional safety measure.
2FA will add the inconvenience of having another added step to your login process buts it’s worth it, it’ll give you peace of mind. Here’s a handy article to help you set up 2FA for your account.
Is your Android phone secure? This checklist will help you make sure that your device’s security in top shape and keep off malware at bay.





























