The continent of Africa is facing a rise in cybercrime activities, and Kenya is right at the centre of this vice. As Western and Eastern African economies become increasingly digital, cyberthreats have surged, now accounting for over 30% of all reported criminal activity in these regions.
With online banking growth in Kenya, banking trojan stealers are becoming an increasingly prevalent cyber threat. Banking Trojans are malicious software that steal financial credentials and send them to a remote server in near real time.
Interpol reports that Kenyan authorities uncovered an online credit card fraud scheme responsible for USD 8.6 million in losses. The group exploited banking system security protocols, using fraudulent scripts to steal funds.
These stolen funds were quickly disbursed via SWIFT to entities in the UAE, Nigeria, and China, then transferred to digital asset institutions operating across multiple jurisdictions. Nearly two dozen arrests were made in an operation labelled Serengeti.
Ambassador Jalel Chelba, AFRIPOL’s Executive Director, said,
“Through Serengeti, AFRIPOL has significantly enhanced support for law enforcement in African Union member states. We’ve facilitated key arrests and deepened insights into cybercrime trends.”
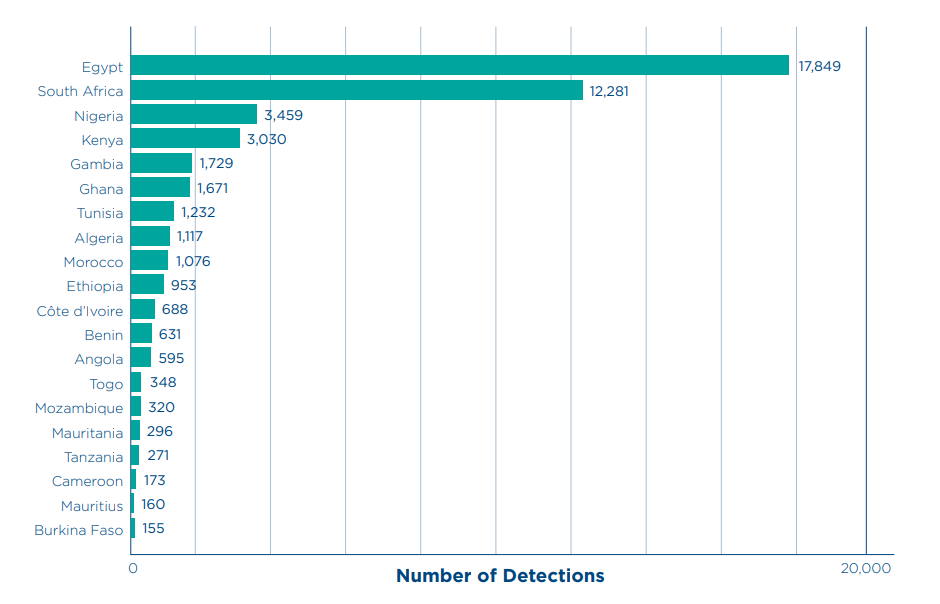
Ransomware is another prevalent cyberthreat facing Kenya. Trend Micro data indicates South Africa and Egypt experienced the highest numbers, with 17,849 and 12,281 detections, respectively. Nigeria followed with 3,459 detections, and Kenya with 3,030.
The Kenyan government was particularly vulnerable to this type of threat.
In July 2024, the Kenya Urban Roads Authority (KURA) experienced a data breach orchestrated by the prominent ransomware group, Hunters International. Approximately 18 GB of data was stolen during the incident. In December 2024, the Kenya Micro and Small Enterprise Authority (MSEA) experienced a cyberattack.
Read: NSSF Denies Allegations of Massive 2.5TB Data Breach
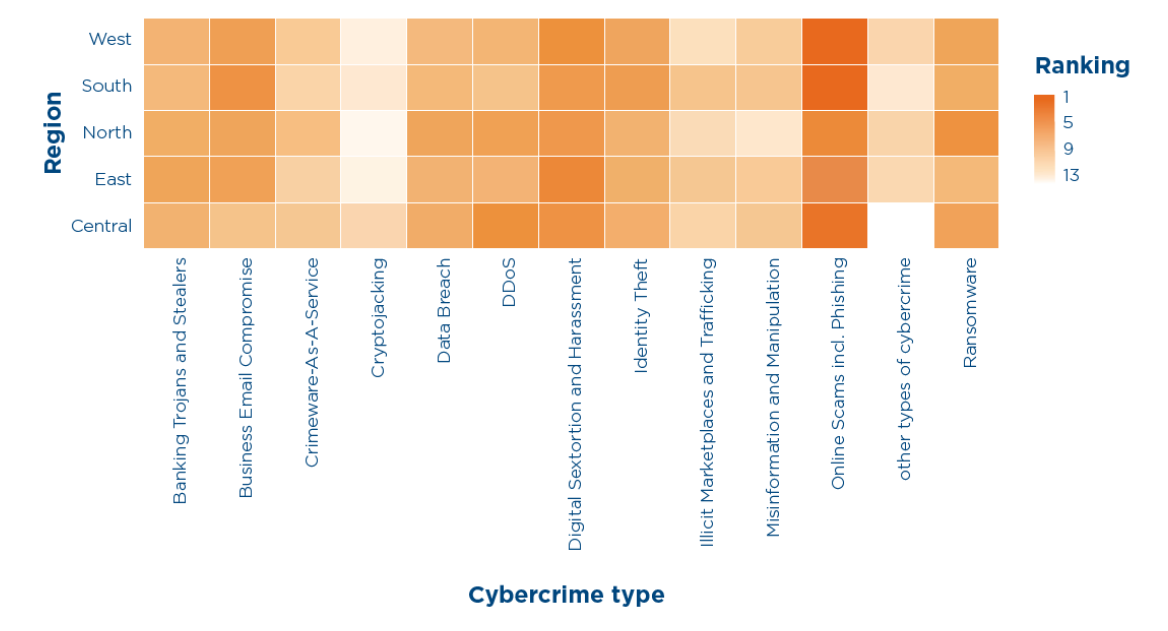
The growing use of social media is also leading to the rise of digital sextortion. This vice is not only affecting Kenya but is a rising cyber threat in the whole of East Africa. Criminals frequently exploit compromising material to extort victims, particularly targeting women and young individuals.
Other frequently reported cybercrimes are phishing and business email compromise (BEC).
Cyberthreats: Rise in East Africa
East Africa urgently requires collaborative efforts and the establishment of strong cybersecurity frameworks. This need is underscored by the fact that in 2024, Ethiopia experienced the highest number of cyberattacks globally, leading the world in malware detections.
Cyberthreats are cross-border, either in terms of similarities or incidents where criminals from different nations cooperate.
However, according to the Interpol report, “While cybercrime routinely crosses national borders, 86 per cent of African member countries surveyed said their international cooperation capacity needs improvement due to slow, formal processes and a lack of operational networks.”
Read: Kenya Detects Over 2.5 Billion Cyber Threats in Three Months
SIM swap fraud, a prevalent cybercrime in Kenya, is now on the rise in Uganda and Tanzania. This scam involves criminals exploiting mobile network vulnerabilities to fraudulently acquire replacement SIM cards. They often achieve this through deception or by colluding with insiders, ultimately hijacking victims’ phone numbers.





























