Cybersecurity threats keep evolving, and now, PDFs have emerged as a surprisingly effective weapon for cybercriminals. With 68% of cyberattacks beginning in inboxes, and 22% of malicious email attachments being PDF-based, the increasing use of this ubiquitous file format has made it a prime target for attackers.
The Prevalence of PDFs in Business and Cybersecurity Threats
Over 400 billion PDFs were opened last year, and 16 billion documents were edited using Adobe Acrobat. Additionally, 87% of organizations rely on PDFs as a standard file format for business communication.
This widespread usage makes PDFs an attractive vehicle for cybercriminals looking to infiltrate organizations through phishing and malicious code.
While PDFs are traditionally viewed as safe and reliable, their increasing exploitation by threat actors has changed the game. Attackers have developed sophisticated techniques to embed malicious content within these files, allowing them to slip past conventional security measures.
Security researchers at Check Point Research have observed that many of these attacks evade traditional security vendors entirely, with zero detections in VirusTotal over the past year.
In this article, we’ll explain why PDFs are such a prime target, how cybercriminals exploit them, and the countermeasures organizations can implement to mitigate risk.
Why PDFs Are a Prime Target for Cybercriminals
PDFs are inherently complex. The PDF specification, ISO 32000, spans nearly 1,000 pages, providing a rich set of features that attackers can exploit.
While users see PDFs as simple, static documents, security tools often struggle to detect malicious activity within them. This complexity allows PDFs to act as a digital “Trojan horse,” appearing harmless while concealing harmful content.
In the past, attackers relied on vulnerabilities in PDF readers (Common Vulnerabilities and Exposures – CVEs) to exploit flaws in software. However, as PDF readers have improved their security—particularly browsers that now open PDFs by default—this method has become less effective.
Consequently, cybercriminals have shifted tactics to rely more on social engineering and hidden malicious links, making it even harder to detect these attacks.
The Anatomy of a PDF-Based Cyberattack
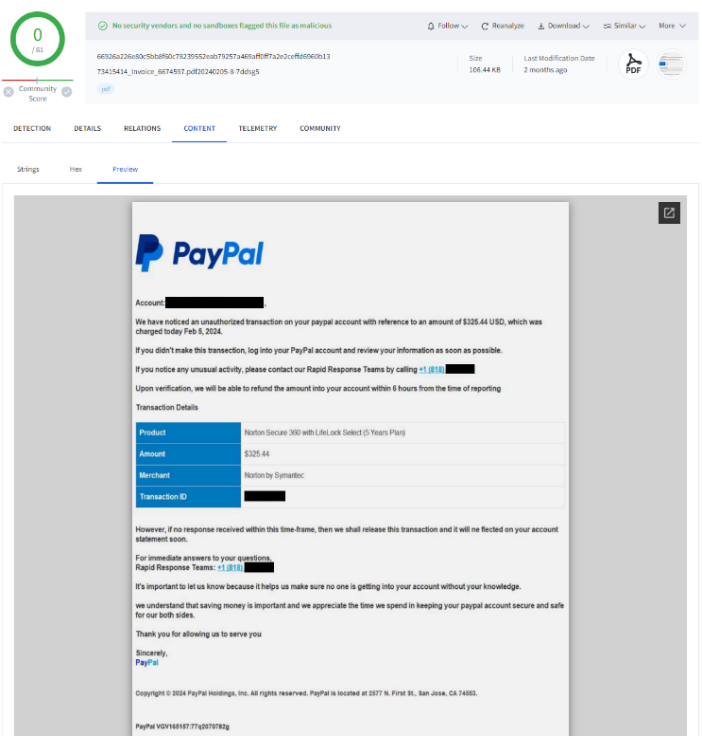
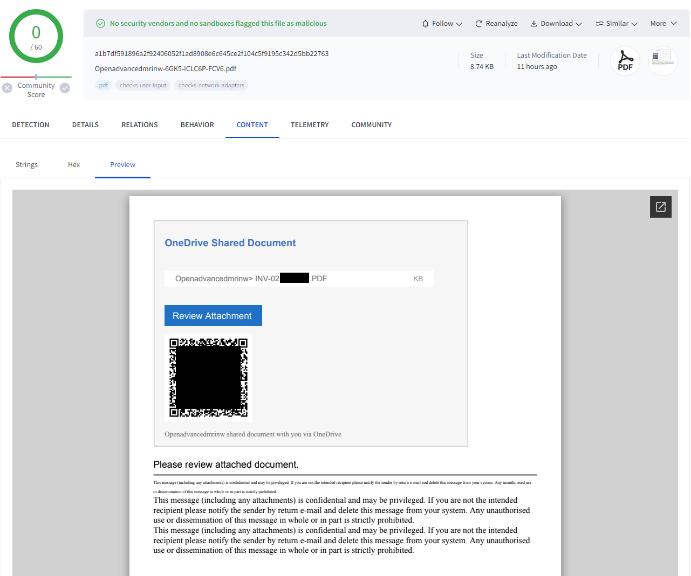
One of the most common cybersecurity attack methods involves embedding malicious links within PDFs. These files often mimic trusted documents from well-known brands such as Amazon, DocuSign, or Acrobat Reader.
When recipients click the links, they are redirected to phishing sites or malware-laden downloads.
Unlike traditional exploits that rely on vulnerabilities in software, link-based PDF attacks are highly effective because they require human interaction. This makes them harder to detect with automated security solutions, which struggle to interpret links in the same way a human would.
Threat actors frequently change the links, images, and content inside PDFs to evade detection from security tools that rely on static signatures or URL reputation databases.
Advanced Evasion Techniques Used by Cybercriminals
To ensure their malicious PDFs bypass security filters, cybercriminals employ sophisticated evasion techniques, including:
1. URL Evasion Techniques
- Using benign redirect services: Attackers mask malicious destinations using trusted platforms like LinkedIn, Bing, or Google AMP to avoid URL blacklisting.
- QR code-based attacks: Instead of clickable links, attackers embed QR codes that victims scan with their phones, bypassing security filters entirely.
- Phone-based scams: Some PDFs instruct users to call a fake support number, leading to social engineering attacks that extract sensitive information.
2. Static Analysis Evasion
- Obfuscation techniques: PDF annotations can be encoded in ways that evade static analysis tools, making it difficult for security solutions to recognize threats.
- Reader-specific exploitation: Since different PDF readers interpret files differently, attackers craft PDFs that exploit reader-specific behaviors, making detection inconsistent.
3. File Obscurement
- Encryption and indirect objects: Attackers use encryption and hidden objects within PDFs to conceal malicious code, making it difficult for scanners to analyze the file’s true contents.
4. Machine Learning Evasion
- Image-based text attacks: By embedding key text inside images, attackers evade text-based security scanners, requiring Optical Character Recognition (OCR) to detect threats.
- Manipulated invisible text: Attackers insert small or invisible text to confuse Natural Language Processing (NLP) models, making automated detection less reliable.
How to Stay Safe from PDF-Based Cyberattacks
While attackers continue to refine their techniques, organizations and individuals can take proactive measures to mitigate risk.
Check Point’s Threat Emulation and Harmony Endpoint solutions offer real-time, zero-day protection against PDF-based attacks, but additional best practices can further enhance security:
1. Verify the Sender
- Always double-check the sender’s email address, especially when receiving unexpected PDFs. Attackers often spoof well-known brands or colleagues.
2. Be Cautious with Attachments
- If a PDF asks you to click a link, scan a QR code, or call a number, treat it as suspicious. When in doubt, avoid interacting with the file.
3. Hover Before Clicking
- Before clicking any link inside a PDF, hover over it to reveal the full URL. Watch out for shortened links or those using redirect services like Bing or Google AMP.
4. Use a Secure PDF Viewer
- Modern browsers and PDF readers have built-in security features. Keep them updated and avoid using outdated or obscure PDF software.
5. Disable JavaScript in PDF Readers
- JavaScript-based attacks are still prevalent. Disable JavaScript in your PDF reader unless absolutely necessary to reduce risk.
6. Keep Security Tools Updated
- Regularly update your operating system, browser, and security software to protect against emerging threats.
7. Trust Your Instincts
- If a PDF looks unusual, contains typos, or asks for sensitive credentials, it’s likely a scam.
PDFs are no longer just harmless document files; they have become a battleground for cybercriminals exploiting their ubiquity and trustworthiness.
By leveraging advanced cybersecurity evasion tactics and social engineering, attackers have turned PDFs into one of the most effective delivery mechanisms for phishing and malware.
Understanding how these attacks work and implementing proactive security measures can significantly reduce the risk of falling victim to PDF-based threats.
Organizations should adopt advanced threat detection solutions like Check Point’s Threat Emulation and Harmony Endpoint to ensure real-time protection against evolving threats.






























