The 2015 Africa Hackon, which was in its second edition after last year’s edition, brought together information security experts and anyone interested in information security at the iHub in Nairobi last Friday. Professor Bitange Ndemo, a former permanent secretary in the ICT ministry and the chief guest, emphasized on the need to protect digital resources. He added that both the government and the private sector needed to invest heavily in cyber security in order to secure the future of non-tech savvy people who are extremely vulnerable to malicious cyber attacks. Furthermore, he insisted that we as a country need to be able to protect our resources hence the need to bridge the gap between security research and innovation by young people and the government. This will ensure that we (as Kenyans) are able to protect ourselves fully without exposing our data to foreign parties.
Information security enthusiasts were treated to mind opening demonstrations by information security experts. They demonstrated several security flaws in our day to day lives as we interact with technology. Importantly, they showed us how to mitigate these flaws and become more secure and urged people to spread the word in order to improve our security.
Bright Gameli, a cyber security engineer, demonstrated among other things, how information we leave behind can be used to potentially attack your system. He showed how social engineering, even in the most secure tech environments can be used to gain access to a system. Who would suspect a normal looking pen to contain a camera and a flash disk? Such a pen can record you inputting your password and essentially give full access to an attacker. He said that we have to be cautious and curious. Do not just open flashy links or shortened ones without having an idea as to where they link to. You may have just given a person full access to your computer controls and files without knowing.
For most people with wireless hotspots in their homes, those networks are poorly secured. We let internet service providers (ISPs) create our networks and retain the default settings. Chrispus Kamau from Alfa Network showed attendees that by exploiting the older version of the SNMP protocol used by most of our ISP’s, an attacker can get information about your network. This is because SNMP (Simple Network Management Protocol) is used to monitor devices connected in a network. An attacker can use this protocol and identify the make and model of devices in your network as well as access the usernames and passwords of the networks. All one has to do is scan an area and get a list of the networks around, the devices used and their passwords. That would mean that a less malicious person can simply have free internet access thanks to you and your insecure home Wi-Fi.
They (infosec experts) have taken steps in notifying ISPs about this but sadly, nothing has changed.
How do you protect your network?
You do not have to be a tech genius to be safe. First, change default names and passwords set up by your ISP. Use complicated ones, change them periodically and be careful as to whom you share your passwords with. Next, employ the use of virtual private networks (VPNs). VPNs secure your data through encryption. You can also use a VPN to access your secure home network while in public WiFi hotspots. Also, as a precaution, don’t trust everyone connected to public Wi-Fi hotspots.
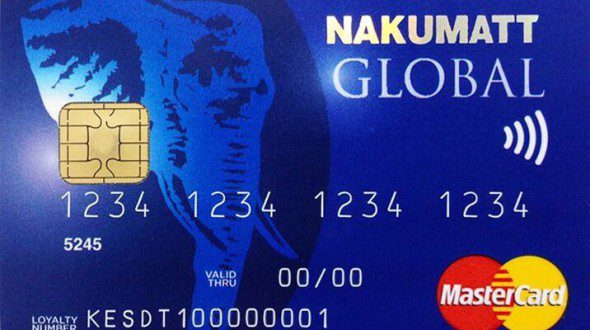
Some of us have mobile devices with near field communication (NFC) cards. Did you know that your NFC card transmits your information to anyone who cares to listen? With an NFC-enabled phone and a simple application, Solomon Nyoike demonstrated how in as little as 2 seconds, he can receive your card information by just being close to you. Yes, like they do in Person of Interest with phones. Details from your card number, its expiry date and latest transactions made by the user are displayed on his phone. With that information and a bit of social engineering, he (and anyone else who cares) can get complete access to your card and use as they please. How do you keep your information safe? He demonstrated that a simple strip of foil will distort the signal, therefore add that to your wallet now.
Other than learning how to secure data, attendees were given a talk by Judy Chebet, a partner at professional services firm Rödl & Partner who specializes in intellectual property law, on ways they can protect their software applications. She identified that many application developers are discouraged from approaching big firms with their work as most of the time their ideas are stolen. She said that with proper and swift action, one can protect their application. She also emphasized on the need for developers to be discrete with their applications and not disclose everything unless a non-disclosure agreement is made.
The takeaway…
With the many security flaws in the cyber space, everyone has a role to play in protecting our resources. If you are a hacker, expose flaws to those affected and teach them on ways to mitigate them. If you are a user, be careful and curious. Don’t take everything as it comes. Everything is exploitable, even VoIP which is easily overlooked. Many firms, shockingly even cyber security firms lose millions from unsecured VoIP connections.
Events like Africa Hackon that bring together experts in the field, industry leaders and technology users are important in spreading the need for information security. Maybe a bigger venue next year?


















