Kenya has recently introduced the National Public Key Infrastructure (NPKI). The NPKI is a critical introduction as more and more day-to-day activities are digitized.
According to the Communications Authority, the national public Key Infrastructure (NPKI) will enhance the adoption of digital certification services and electronic transactions across the public sector.
The National Public Key Infrastructure (NPKI) is managed by the Communications Authority of Kenya (CA).
What is a Public Key Infrastructure?
A public Key Infrastructure (PKI) refers to a system for the creation, storage, and distribution of digital certificates which are used to verify that a particular public key (online identity) belongs to a certain entity.
In brief, a PKI makes you know the person or institution you are dealing with online is verified and legitimate. It will help in electronically identifying people, entities, organizations and machines in a reliable way.
During the ICT week, Cabinet Secretary Eliud Owalo identified verified online identity as a means to boost trust and push the growth of ecommerce.
Mr. Owalo said, “However, as we prospect on e-commerce, the challenges with online transactions point to the need to continually educate consumers on challenges that abound, to enhance their confidence in online platforms.
We are now rolling out the National Public Key Infrastructure (NPKI) to enhance trust by issuing digital signatures and certificates.”
Thus, effective use of the NPKI will ensure confidentiality, integrity, authentication, and non-repudiation in online transactions among Kenyans.
NPKI Infrastructure Scheme
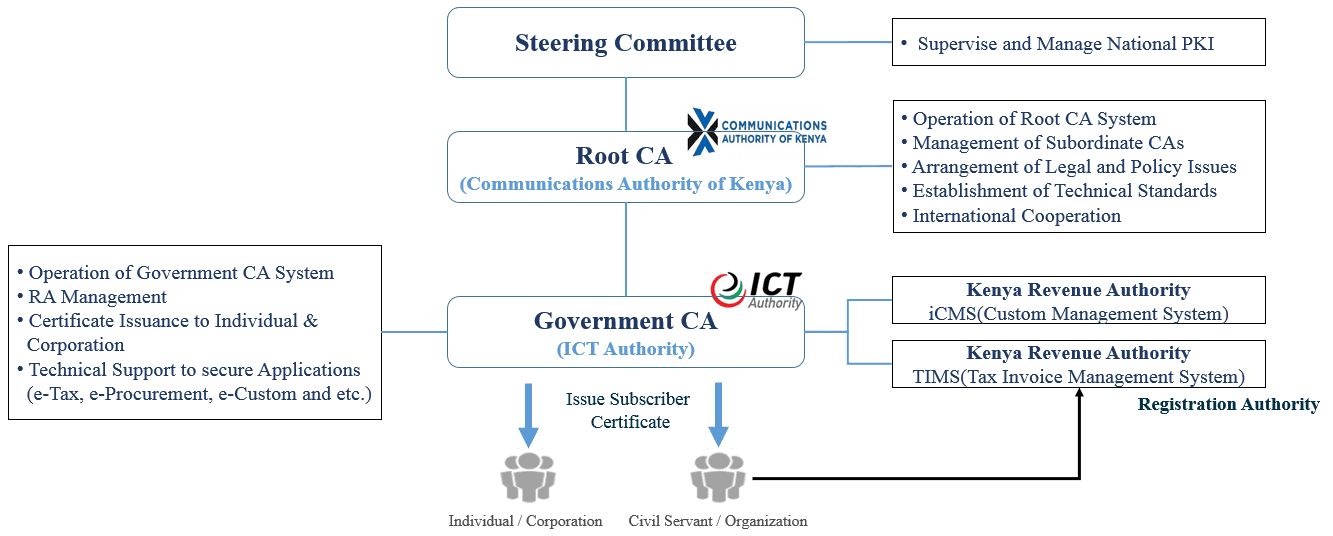
The Governments National (Public Key Infrastructure) PKI scheme consists of four envisaged independent organizational structures and agencies. These are;
(a) Steering committee: The Steering committee has a role to supervise, manage and make strategic decisions related to National PKI.
(b) Root Certification Authority (CA): Communications Authority (CA) has the role of a Root CA which supervises and regulates Certification Authorities (CAs).
(c) A Government Certification Authority (GCA): The ICT Authority has a role of Government Certification Authority (CA) which issues digital certification subscriber.
(d) Registration Authority (RA): An E-Government service provider assumes the role of a Registration Authority, which is to identify and register subscribers of digital certificates to Government Certification Authorities (CAs). (.e.g. Ministries and other user agencies). This role will be played by the ICT Authority
NPKI Licensing
The Kenyan NPKI is a technical infrastructure that comprises a Root Certification Authority (RCA) and a Certification Authority (CA). The government certification authority is managed by the ICT Authority.
The NPKI is the basis for licensing of Electronic Certification Service Providers (E-CSPs). E-CSPs then offer the online certification service to the general public.
The E-CSPs are vetted, licensed and regulated by the Communications Authority. Additionally, Digital Certificates issued by an accredited E-CSP are globally recognized and trusted.
Currently, the CA has licensed 3 private E-CSPs and the ICT Authority (ICTA) as the Electronic Certification Service Provider (E-CSP) for the Government of Kenya.
The ICT Authority is expected to offer the Digital Certificates services to various government agencies among them the Kenya Revenue Authority, the National Transport and Safety Authority, Ministry of Lands and Physical Planning and the National Treasury and more.
The 3 private E-CSPs are Geda Limited, Tendaworld Ltd, and Emudhra Technologies Limited. The authority is in the process of accrediting 6 others. Requirements to apply for Electronic Certification Service Provider (E-CSP) are similar to a license for a Network Facilities provider.
Certifcations will be subject to review and renewal. Furthermore, breach of terms will lead to the revocation of the digital certificate.



















